A 90 percent drop in fraud leads to a 2.5x increase in sales. This was PUMA’s result after its agency worked directly with a key partner to close a cash-on-delivery fraud loophole.
The breakthrough wasn’t a better fraud filter. It happened when their agency engaged directly with the partner to find the loophole together.
And they are not the only ones worried about this. According to impact.com’s State of Affiliate Marketing Report, nearly a quarter of all brands cite partner quality as a major concern, while 21 percent are in a constant battle with fraud.
And yet brands keep pouring money into a channel they fundamentally don’t trust.
The default response has been a technological arms race. But this approach misses the core lesson from brands like PUMA, and what the most successful managers already know.
The partnership managers who prevent the most affiliate fraud aren’t the ones with the best fraud-detection tools. They’re the ones who actually know their partners.
As brands head toward 2026, protecting your investment requires a new strategy. This guide provides that defense—one centered not on technology alone, but on the actionable strategies that come from turning your partners into your most powerful allies.
5 defense pillars against affiliate marketing scams
The scams detailed below are sophisticated, fast, and designed to be invisible. But they all rely on the same weakness: the anonymity of a purely transactional relationship. Your defense, therefore, cannot be a single tool but a multi-layered strategy rooted in the principle that knowing your partners is your most powerful asset.
1. Shift to post-conversion vetting (and expose the AI mimics)
The first line of defense is recognizing that the game has changed. Pre-conversion metrics are no longer reliable indicators of partner quality. To catch sophisticated AI, you must shift your focus from how a customer converts to what they do next.

This requires a fundamental change in how you validate partners, moving from automated approval to active, post-conversion vetting.
This new reality makes your performance metrics work against you. The table below summarizes the threat and the red flags to watch for.
| Impact on your program | Key red flags |
| Paying for “ghost” customers: You are paying full commissions for conversions from users who don’t exist, leading to zero chance of repeat purchases or lifetime value. | High chargeback and refund rates: A spike in refunds or chargebacks indicates the “customers” were never real and the purchases were fraudulent. |
| False confidence in performance: This fraud makes your worst partners look like your best, leading you to trust and invest in completely fabricated performance data. | Zero Customer Lifetime Value (LTV): The initial “customer” was a ghost; they never returned to make a repeat purchase or engage further with your brand. |
| Complete invalidation of LTV models: Because the “customers” aren’t real, any models you build for predicting customer lifetime value are fundamentally corrupted. | No post-conversion engagement: Users sign up for a service but never log in again, activate features, or interact with your app. |
Unmasking AI scammers: A strategic defense against fraudulent bot traffic
1. Vet partners beyond application
Before a partner drives volume, get to know them. A partner who can’t clearly articulate their traffic sources or promotional strategy on a brief call is a major red flag—no matter how good their data looks. If their story feels off, trust your judgment. This human-centric approach is your most crucial defense.
2. Track post-conversion metrics
Shift your analysis to what happens after the click. Use robust analytics to monitor post-conversion metrics like chargeback rates, customer lifetime value (LTV), and actual user engagement. These long-term outcomes are difficult and expensive for AI to fake at scale, making them reliable indicators of fraud.
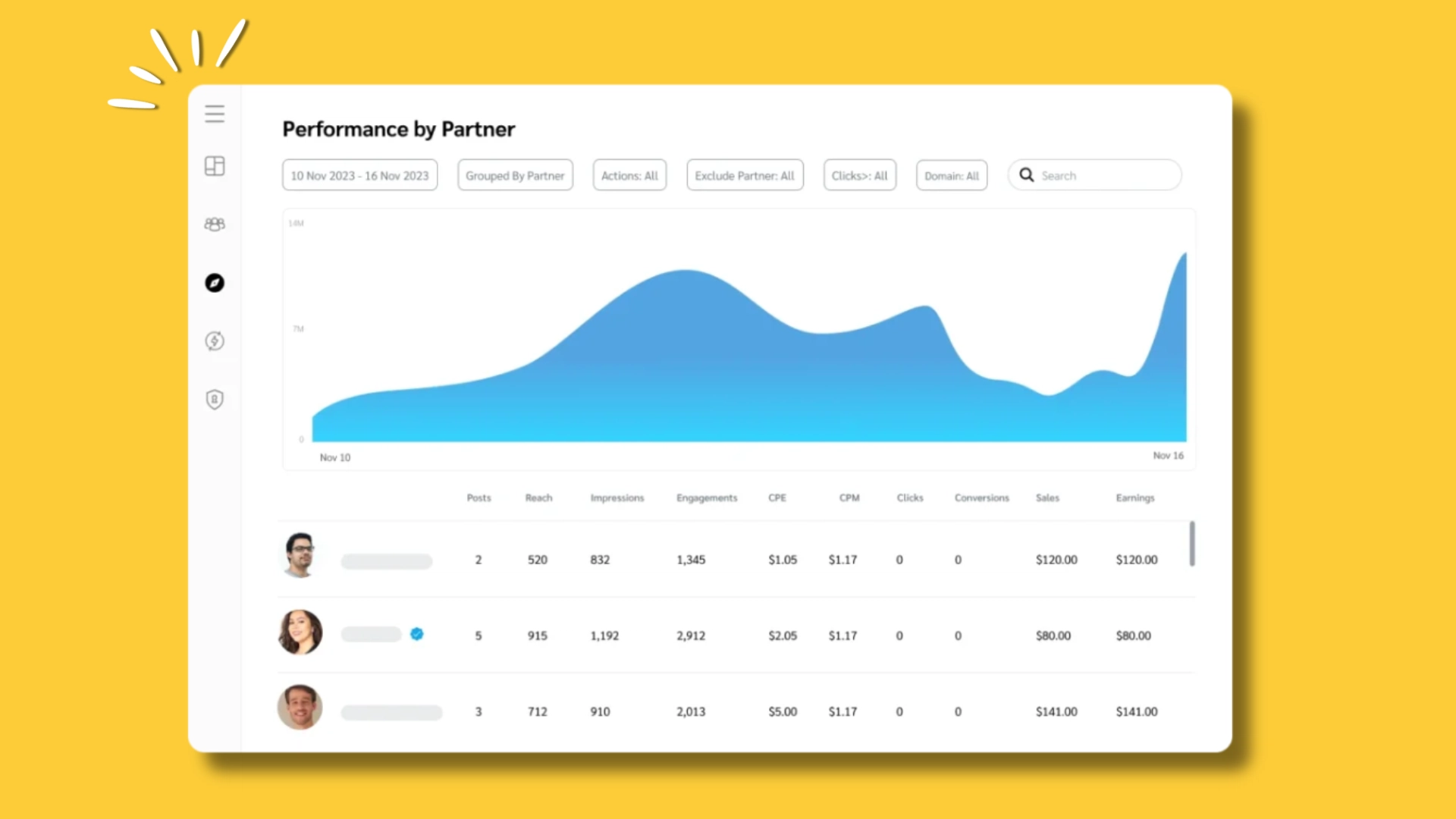
Use Performance reports to gain a comprehensive view of campaign impact and ROI
3. Deploy AI-powered bot detection
Fight sophisticated AI with more sophisticated AI. Automated solutions from platforms like DataDome analyze subtle behavioral anomalies that are invisible to the human eye. As the ad fraud solution Anura notes, it can guarantee 99.999% accuracy in identifying fraudulent visitors, making these tools a critical frontline defense.
4. Add smart friction at critical points
Implement strategic verification steps to filter out bots without harming the user experience.
- Background scoring: Use tools like Google reCAPTCHA v3.
- High-value actions: Secure them with Two-Factor Authentication (2FA).
- Bulk signups: Prevent them with simple email verification.
2. Mandate promotional transparency (and counter the arbitrage bots)
The second pillar of defense is demanding total transparency in how and where partners promote your brand.

Agentic search arbitrage thrives in opacity, where fraudsters can exploit your program without adding any value. By requiring partners to be open about their methods, you shut down this channel for abuse.
This threat makes it appear as though a partner is driving significant traffic, when in reality, they are just a “middleman” siphoning away your margin. The table below breaks down the threat and how to spot it.
| Impact on your program | Key red flags |
| Margin erosion via cannibalization: You pay a commission for a customer you would have acquired anyway through your own direct or organic channels, directly shrinking your profit margin. | Traffic from generic sources: Referral reports show traffic coming from URL shorteners (like bit.ly) or generic landing page domains instead of the partner’s actual website. |
| Devaluation of your brand: Your brand is promoted on low-quality, “thin content” landing pages you have no control over, which is damaging your reputation. | Mismatched Geo-location: You see clicks and traffic from countries or regions where the partner claims they have no audience. |
| Misleading channel growth: Your affiliate channel’s performance is artificially inflated with low-value activity, leading you to misallocate budget away from truly incremental partners. | High bounce rates and low conversion: Traffic is high, but users don’t engage, convert, or spend much time on your site because they weren’t properly qualified. |
Countering arbitrage scams: A defense built on promotional transparency
Your defenses should focus on enforcing transparency and using your tracking capabilities to verify what partners tell you.
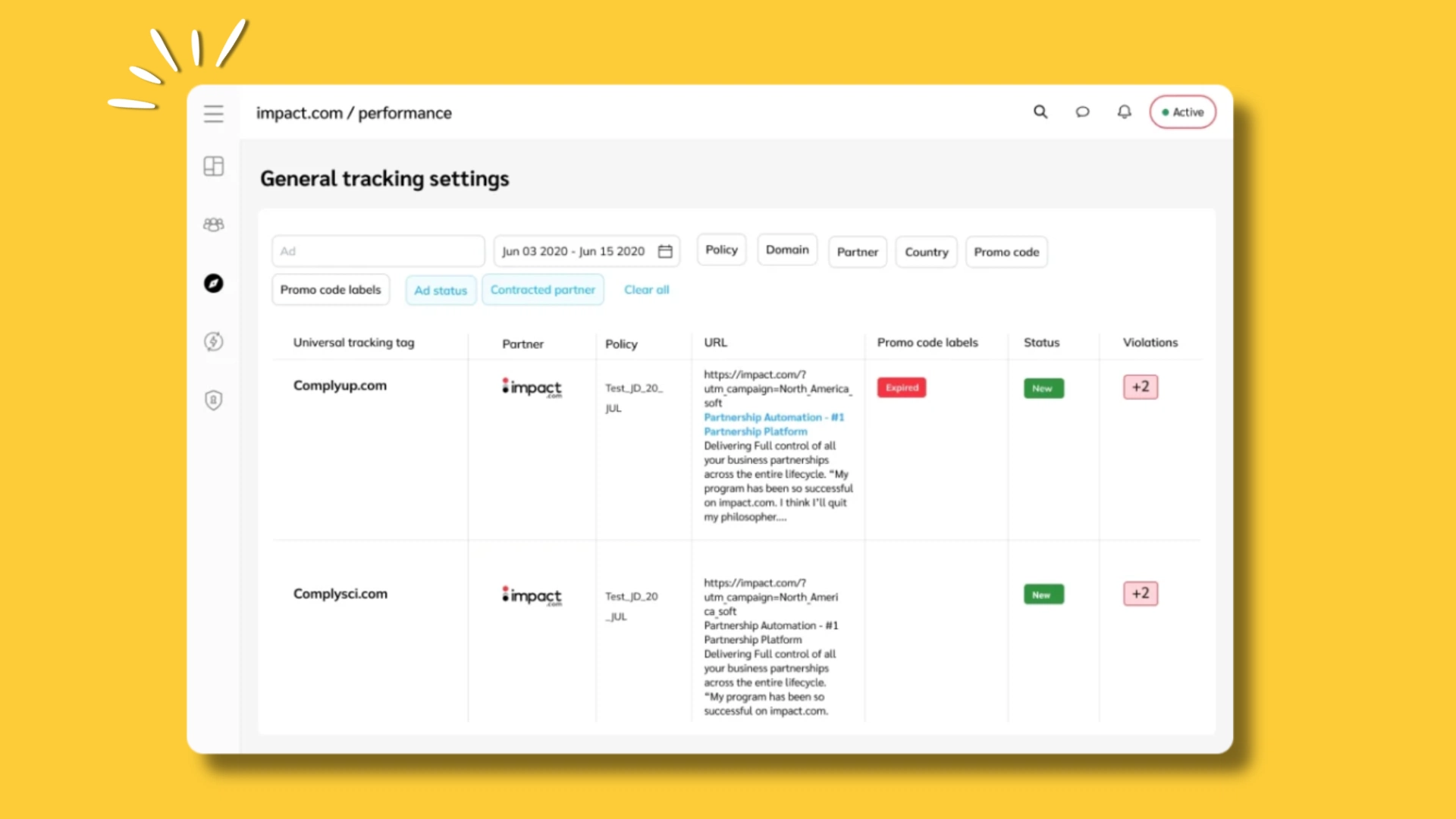
1. Require full promotional transparency in your terms
This is non-negotiable. Your program’s terms and conditions must explicitly require partners to disclose all promotional methods and domains. Conduct audits where you ask partners to provide screenshots or live links to their promotional content. A partner who is unwilling to be transparent is not a true partner.
2. Enforce brand bidding & keyword restrictions
Clearly define your keyword bidding policy. Prohibit partners from bidding on your branded terms, misspellings, or any other keywords you reserve for your own team. Use brand monitoring tools to automatically detect and flag violations, giving you the evidence needed to enforce your terms.
3. Monitor brand sentiment across promotions.
Beyond just monitoring for keyword violations, it’s crucial to understand the context and quality of the promotions themselves. Using tools like Sentiment Analysis allows you to tap into the public conversation surrounding your brand in relation to partner content. A sudden spike in negative sentiment tied to an affiliate’s campaigns can be an early warning sign of low-quality promotions or misaligned messaging that devalues your brand—a red flag that traffic volume and conversion metrics alone will never show you.
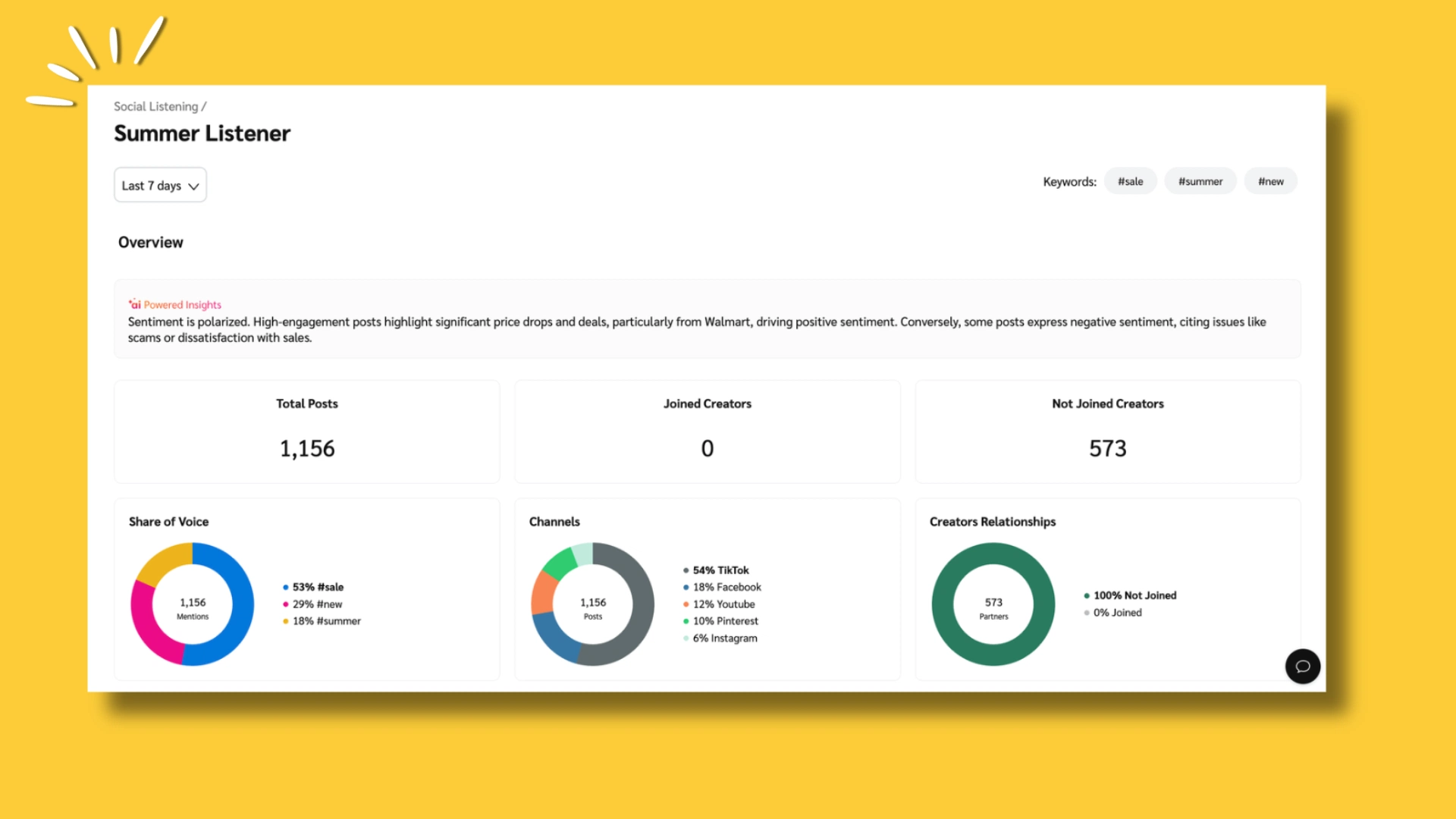
Sentiment Analysis helps you feel the pulse of online conversations
4. Use tracking parameters to verify sources
Mandate that partners use specific sub-IDs or UTM parameters for each campaign or traffic source. This forces them to segment their traffic and gives you a clear, granular view of where users are actually coming from, making it much harder to hide low-quality arbitrage traffic.
3. Define and enforce your attribution rules (and stop last-second theft)
The third pillar of a strong defense is establishing crystal-clear rules of engagement for attribution. Attribution theft via browser extensions preys on ambiguity.

By creating and enforcing strict terms around what constitutes a valid referral, you can disqualify bad actors and protect the commissions of your true value-adding partners.
This type of fraud not only steals from you but also from your honest partners, damaging trust in your program. The table below outlines the threat and the key signals to watch for.
| Impact on your program | Key red flags |
| Theft from your best partners: This fraud directly steals earned commissions from your high-value content partners, demotivating them and damaging trust in your program. | Impossibly short click-to-conversion times: A user “clicks” and “converts” in under a second. This is a tell-tale sign of an automated injection on the checkout page. |
| Rewarding zero-value “partners”: You end up paying your most valuable commissions to actors who contributed nothing to the customer journey, reinforcing a broken attribution model. | A spike in commissions for one partner: A single affiliate suddenly accounts for a large share of your sales, often without a corresponding identifiable traffic source. |
| Poisoned partner leaderboards: Your internal reports will incorrectly show a valueless extension as a “top performer,” masking the true contributions of your best affiliates. | Complaints from other affiliates: Honest partners may reach out to you, asking why they aren’t being credited for sales they know they drove. |
Preventing commission theft: A strategic defense against attribution hijacking
Your defenses must combine clear policies with active monitoring to ensure the rules are being followed.
1. Build a “zero tolerance” policy for cookie stuffing
Your affiliate agreement must explicitly forbid cookie stuffing, adware, and forced clicks. State that any partner found using these methods will be immediately removed from the program, and all pending commissions will be forfeited. This clarity eliminates any gray area.
2. Audit your “top-performing” partners
If a new partner suddenly becomes a top earner overnight without a clear traffic source, that’s a red flag. Reach out to them. Ask them to walk you through their user journey and explain their value. A legitimate partner will be happy to do so, while a fraudster will be evasive.
3. Monitor click-to-conversion timelines
Use your affiliate platform’s reporting tools to identify partners with consistently low click-to-conversion times. While not always fraudulent on its own, a pattern of sub-five-second conversions is highly indicative of attribution theft and warrants a direct conversation with the partner.
4. Fortify your tracking integrity (and block server-side attacks)
The partners you’ve identified are only valuable if you can coordinate at scale, which is why fortifying your tracking integrity matters
As tracking moves away from the browser and toward server-to-server (S2S) connections, your fourth defensive pillar must be a commitment to technical due diligence.

S2S fraud happens when you trust a partner’s servers without verifying their data. The defense is to know your partner’s technical capabilities and validate that the data they send is legitimate.
This fraud is invisible on the front end and can only be caught by scrutinizing the data itself. You are, in effect, trusting that the partner’s server is telling you the truth.
| Impact on your program | Key red flags |
| Paying for fabricated events: You pay commissions for conversions that are pure fiction—they were never real and were manufactured entirely on a fraudster’s server. | Missing or mismatched IP addresses: The conversion event lacks a user IP address, or the IP address doesn’t match the click’s geo-location. |
| Corruption of conversion data: Unlike other frauds that manipulate real traffic, this injects completely fake events, making your core conversion data fundamentally untrustworthy. | Anomalous event sequencing: You receive a conversion event from a partner before you’ve registered an initial click, which is logically impossible. |
| Undermined trust in server-side tracking: This fraud erodes confidence in your most reliable and future-proofed tracking method, creating internal resistance to adopting it. | High volume of events with no device data: A large number of conversions lack standard user-agent or device information, suggesting they weren’t generated by a real user. |
Blocking server-side attacks: A technical defense for S2S tracking integrity
Your defenses must be technical, creating a system of verification that assumes nothing and validates everything.
1. Conduct technical vetting for S2S partners
Knowing your partner in an S2S world means knowing their tech stack. Before enabling S2S tracking for any partner, have your technical team conduct a due diligence call with their developers. This vetting process ensures they have a legitimate, well-understood system for firing conversions and serves as a powerful deterrent to fraudsters.
2. Require a Click ID Match for all conversions
Ensure that every S2S conversion event sent by a partner includes the unique click ID that was generated when the user first clicked their link. If your server receives a conversion postback with an invalid or missing click ID, reject it automatically.
3. Use shared secrets or cryptographic signatures
Never use an open, unauthenticated S2S endpoint. Require partners to include a private token or “shared secret” in their postbacks to verify their identity. For even greater security, implement cryptographic signatures, which ensure the converted data has not been tampered with in transit.
4. Monitor your server logs for anomalies
Actively monitor your incoming server logs for the red flags mentioned in the table above. Look for patterns like high volumes of conversions from a single IP address, postbacks with missing data, or impossible event sequences. Automate alerts for these patterns to detect potential fraud in real time.
Future-proof your program with a modern, reliable approach to tracking.
5. Unify your attribution view (and expose the multi-device shell game)
You can’t truly know your partners if you’re missing half their contributions. This is exactly what happens when attribution is fragmented across devices. Unifying your view exposes who’s actually driving results.
The final pillar of your defense is to move from fragmented, device-level tracking to a unified, person-level view of the customer journey.
Cross-platform fraud thrives in the gaps between devices where bad actors can hide their trail. By using a platform that connects the dots, you can clearly see a partner’s true influence and shut down this sophisticated shell game.
This method makes a fraudulent partner appear sophisticated, tricking you into paying for a conversion they played no part in. The table below breaks down how to spot this activity.
| Impact on your program | Key red flags |
| Paying a premium for fake journeys: You pay high-value commissions (e.g., for a desktop sale) that were initiated by a worthless, fraudulent click on a different device (e.g., a mobile click farm). | Illogical journey timelines: The data shows a user clicking a mobile ad and converting on a desktop seconds later—a physically impossible sequence. |
| Deeply flawed customer journey insights: This fraud poisons your understanding of how users behave across devices, leading you to build your marketing strategy around a completely false narrative. | High mobile clicks, zero mobile conversions: A partner drives tens of thousands of mobile clicks but has a 0% conversion rate on that device, yet gets credit for desktop sales. |
| Strategic misinvestment in channels: You are tricked into over-investing in what appears to be a sophisticated, high-performing cross-device partner, taking budget away from those who drive real value. | Mismatched geographies: The initial click originates from one country, while the conversion event happens in another. |
Exposing multi-device fraud: A defense built on unified attribution
Your defenses must evolve beyond simple click tracking to embrace a holistic view of partner value.
1. Establish a single source of truth with cross-device tracking
The essential first step is to eliminate blind spots. You must use a tracking solution that can trace a single user’s journey across their mobile, desktop, and app interactions. This creates a unified “customer profile” and provides the foundational data needed to spot the illogical journeys that are the hallmark of cross-platform fraud.
2. Move beyond last-click with multi-touch attribution models
Last-click attribution is the fraudster’s best friend. Shift to a multi-touch attribution model (e.g., linear, time-decay, or U-shaped) that distributes credit across all contributing partner touchpoints. This inherently devalues the fraudulent last-second click and rewards the partners who actually introduced and nurtured the user earlier in their journey.
3. Prove true influence with incrementality testing
An attribution model shows you what happened, but incrementality testing tells you if it mattered. Use methodologies like lift studies to measure a partner’s causal impact by comparing a test group exposed to their ads against a control group. This isolates the true, incremental value a partner drives, making it impossible for a non-value-add fraudster to hide.
4. Align commissions with a partner’s incremental value
Use the insights from your attribution and incrementality data to build smarter commissioning rules. If a partner’s touchpoint is proven to have low incremental value, pay them a proportionally smaller commission. By directly tying rewards to proven value, you make the arbitrage at the heart of cross-platform fraud unprofitable.
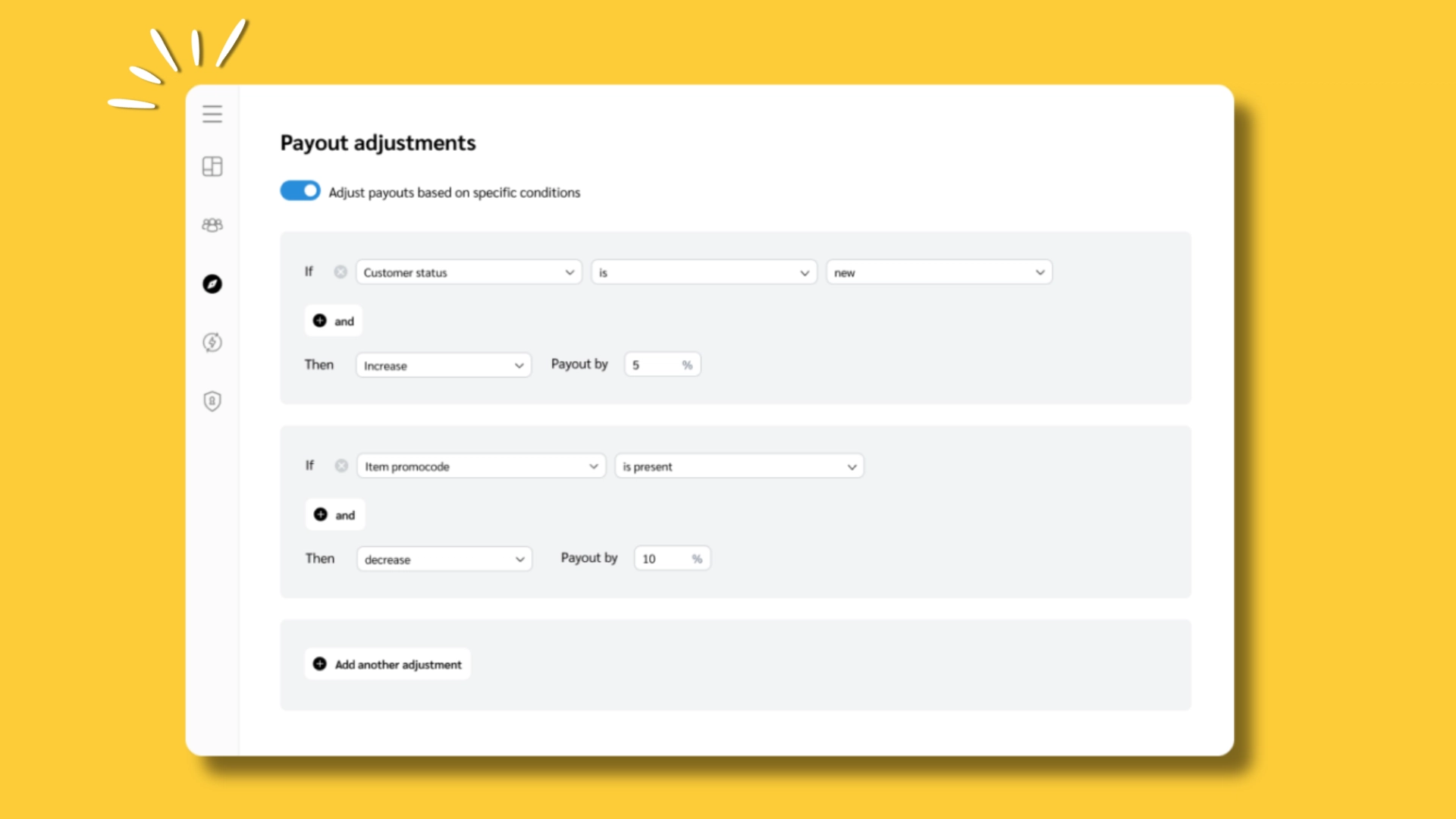
Use Dynamic Payouts to automatically adjust partner commissions
Frequently asked questions
A key example is AI human mimicry. This is where a fraudulent partner uses sophisticated bots to fake an entire customer journey, from click to checkout. Your data shows impressive sales, but these “customers” don’t exist, leading to high refund rates and zero lifetime value. Another common example is attribution theft, where a browser extension injects its tracking cookie seconds before a purchase, stealing the commission from the partner who actually earned it.
You detect it by shifting from pre-conversion metrics to post-conversion analysis. Instead of just looking at clicks and sales, you must track what happens after the sale: monitor refund rates, customer lifetime value (LTV), and user engagement per partner. Also, watch for key red flags like impossibly short click-to-conversion times (under five seconds), traffic from generic or suspicious sources, and a sudden spike in commissions for one partner without a clear promotional strategy.
Three main factors are driving the increase. First, the widespread accessibility of AI tools allows scammers to create more sophisticated bots. Second, the move toward server-to-server (S2S) tracking created new vulnerabilities that fraudsters can exploit with fake conversion signals. Finally, complex, multi-device customer journeys create attribution gaps, allowing scammers to take credit for sales they didn’t influence.
Your next conversation, powered by a smarter platform
PUMA’s agency didn’t find the cash-on-delivery loophole by running a better fraud report. They found it by calling their partner and asking how it worked.
That conversation, not the technology that enabled it, was the breakthrough. The five pillars in this guide are designed to make you ready for yours. Not to replace the conversation, but to give you the data that makes it productive. That includes the post-conversion anomaly that prompts the call, the traffic transparency question you now know to ask, the click-to-conversion timeline that doesn’t add up.
The brands that will lose the least to fraud in 2026 aren’t the ones with the most sophisticated filters. They’re the ones whose partners pick up the phone.
Explore our suite of resources to master affiliate fraud detection and prevention:
- Addressing quality and brand safety in performance marketing (blog)
- Affiliate fraud prevention: 6 ways to protect your brand from scammers (blog)
- AI-powered sentiment that drives real results (one-sheet)
- Measure the real impact of your partnership program (worksheet)
- Beyond basic tracking: 5 data-driven strategies to transform your affiliate program’s ROI (blog)




